Penetration Testing, Pen Testing, Red Teaming, Security Assessment, IT Health Check and Ethical Hacking are common phrases that describe what we do, that ultimately all mean the same thing – whether or not a determined adversary can gain unauthorised access to your systems.
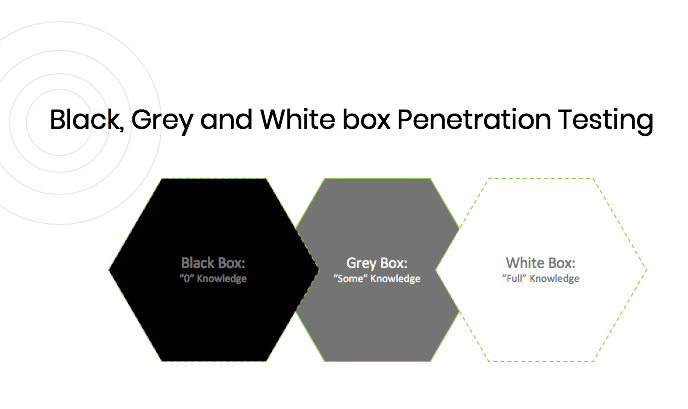
This can be further broken down into Black, Grey and White box Penetration Testing:
- Black Box Penetration Testing, is where you give us no information, thus simulating how a real criminal might attempt to exploit vulnerabilities within your systems.
- Grey Box Penetration Testing is where you give us partial information, somewhere in between White and Black box, although there is no specific definition. Think of it more as a prompt, to guide us toward systems we should be focussing effort upon.
- White Box Penetration Testing, is where you give us all the information we ask for, potentially including source code, to understand where vulnerabilities exist in your systems, that may or may not be exploitable.
We also recommend considering scenario based testing, to ensure our efforts remain focussed, for example:
- What damage can an adversary with no information or credentials do to your systems? Both from the outside and inside?
- What if an authorised user decided to try and hack you?
- How far might ransomware propagate if one machine were infected?
- What risk would a stolen laptop or mobile pose?
Another concept to consider, is that Penetration Testing is but one recommended security control of many. There’s little point spending time, effort and money on a complex Penetration Testing programme, if blue team efforts are ignored. So the blue team are on your side, trying to defend against cyber security attacks, be this through a series of automated security controls (eg firewalls, IPS, WAF, SIEM, vulnerability and patch management); and the red team are the malicious actors that are trying to gain access.
In short, don’t spend time, money and effort Penetration Testing your corporate web application, if the real risk resides in a lack of internal blue team controls.
At 2|SEC Consulting, we’re here to help you at every step of the way.
If you would like to learn more about our services, please click here or contact us at marketing@2-sec.com or call our office on 020 7877 0060.